About Apple security updates

Jul 20, 2021 Yosemite 10.1.2; Mavericks 9.1.3; and older. The default browser for Apple devices and there are no official versions of Safari for other devices. Apple no longer supports Mac OS 10.14 for Macbooks older than 2012. No support for WebSQL; No support for Legacy Safari Extensions; Can't update Safari on OS X 10.5.

For our customers' protection, Apple doesn't disclose, discuss, or confirm security issues until an investigation has occurred and patches or releases are available. Recent releases are listed on the Apple security updates page.
- Dec 14, 2018 However, anyone running OS X Yosemite 10.10.5 specifically should avoid updating to iTunes 12.8.1 for now, as users across the MacRumors Forums, Twitter, Reddit, and Stack Exchange report that the.
- However, anyone running OS X Yosemite 10.10.5 specifically should avoid updating to iTunes 12.8.1 for now, as users across the MacRumors Forums, Twitter, Reddit, and Stack Exchange report that the.
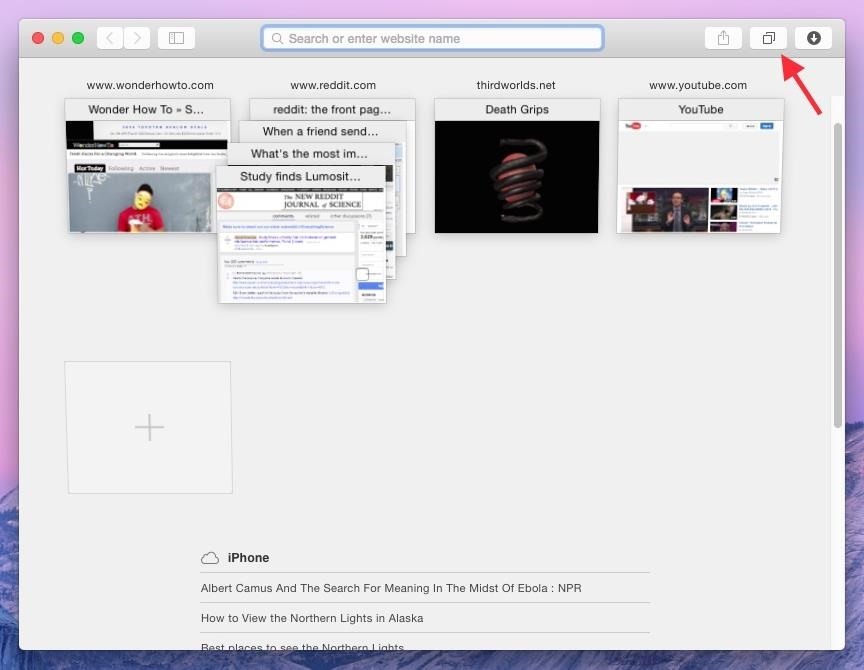
- Safari is included with your Mac. To keep Safari up to date, install the latest macOS updates. The most recent version of macOS includes the most recent version of Safari. If you deleted Safari and don't have a backup, reinstall macOS to put Safari back in your Applications folder. Reinstalling macOS doesn't remove data from your computer.
For more information about security, see the Apple Product Security page. You can encrypt communications with Apple using the Apple Product Security PGP Key.
Apple security documents reference vulnerabilities by CVE-ID when possible.
Safari 10.1.1
Released May 15, 2017
JavaScriptCore
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Processing maliciously crafted web content may lead to unexpected application termination or arbitrary code execution
Description: Multiple memory corruption issues were addressed through improved memory handling.
CVE-2017-7005: lokihardt of Google Project Zero
Entry added June 9, 2017
Safari
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Visiting a maliciously crafted webpage may lead to an application denial of service
Description: An issue in Safari's history menu was addressed through improved memory handling.
CVE-2017-2495: Tubasa Iinuma (@llamakko_cafe) of Gehirn Inc.
Safari
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Visiting a malicious website may lead to address bar spoofing
Description: An inconsistent user interface issue was addressed with improved state management.
CVE-2017-2500: Zhiyang Zeng and Yuyang Zhou of Tencent Security Platform Department
CVE-2017-2511: Zhiyang Zeng of Tencent Security Platform Department
WebKit
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues were addressed with improved memory handling.
CVE-2017-2496: Apple
CVE-2017-2505: lokihardt of Google Project Zero
CVE-2017-2506: Zheng Huang of the Baidu Security Lab working with Trend Micro’s Zero Day Initiative
CVE-2017-2514: lokihardt of Google Project Zero
CVE-2017-2515: lokihardt of Google Project Zero
CVE-2017-2521: lokihardt of Google Project Zero
CVE-2017-2525: Kai Kang (4B5F5F4B) of Tencent’s Xuanwu Lab (tencent.com) working with Trend Micro’s Zero Day Initiative
CVE-2017-2526: Kai Kang (4B5F5F4B) of Tencent’s Xuanwu Lab (tencent.com) working with Trend Micro’s Zero Day Initiative
CVE-2017-2530: Wei Yuan of Baidu Security Lab, Zheng Huang of the Baidu Security Lab working with Trend Micro’s Zero Day Initiative
CVE-2017-2531: lokihardt of Google Project Zero
CVE-2017-2538: Richard Zhu (fluorescence) working with Trend Micro's Zero Day Initiative
Safari Yosemite 10.10.5 Windows 10
CVE-2017-2539: Richard Zhu (fluorescence) working with Trend Micro's Zero Day Initiative
CVE-2017-2544: 360 Security (@mj0011sec) working with Trend Micro's Zero Day Initiative
CVE-2017-2547: lokihardt of Google Project Zero, Team Sniper (Keen Lab and PC Mgr) working with Trend Micro's Zero Day Initiative
CVE-2017-6980: lokihardt of Google Project Zero
CVE-2017-6984: lokihardt of Google Project Zero
Entry updated June 20, 2017
WebKit
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue existed in the handling of WebKit Editor commands. This issue was addressed with improved state management.
CVE-2017-2504: lokihardt of Google Project Zero
WebKit
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue existed in the handling of WebKit container nodes. This issue was addressed with improved state management.
CVE-2017-2508: lokihardt of Google Project Zero
Safari For Yosemite 10.10.5
WebKit
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue existed in the handling of pageshow events. This issue was addressed with improved state management.
CVE-2017-2510: lokihardt of Google Project Zero
WebKit
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Description: A logic issue existed in the handling of WebKit cached frames. This issue was addressed with improved state management.
CVE-2017-2528: lokihardt of Google Project Zero
WebKit
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Processing maliciously crafted web content may lead to arbitrary code execution
Description: Multiple memory corruption issues with addressed through improved memory handling.
Safari Yosemite 10.10.5 Mac
CVE-2017-2536: Samuel Groß and Niklas Baumstark working with Trend Micro's Zero Day Initiative
WebKit
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: Processing maliciously crafted web content may lead to universal cross site scripting
Safari Yosemite 10.10.5 Free
Description: A logic issue existed in frame loading. This issue was addressed with improved state management.
CVE-2017-2549: lokihardt of Google Project Zero
WebKit Web Inspector
Available for: OS X Yosemite 10.10.5, OS X El Capitan 10.11.6, and macOS Sierra 10.12.5
Impact: An application may be able to execute unsigned code
Description: A memory corruption issue was addressed with improved memory handling.
CVE-2017-2499: George Dan (@theninjaprawn)
Additional recognition
Safari
We would like to acknowledge Flyin9_L (ZhenHui Lee) (@ACITSEC) for their assistance.